What we cover
What is penetration testing?
Penetration testing, also known as pen testing or ethical hacking, is the practice of testing a computer system, network or web application to find security vulnerabilities that an attacker could exploit. The goal of penetration testing is to identify security weaknesses before a malicious hacker can find and take advantage of them.
Pen testing helps organizations improve their security posture by proactively finding and fixing vulnerabilities. It complements other cybersecurity measures like firewalls, antivirus software and intrusion detection systems. Regular pen testing is crucial for organizations that handle sensitive data like financial information, healthcare records and personal information.

How does it work?
Penetration testing typically follows these steps:
- Planning: The pen testers and the organization decide the scope and rules of engagement. The testers gather information about the targeted systems and networks.
- Discovery: The testers use open source intelligence and tools to map out the organization’s digital footprint and find potential points of entry.
- Attack: The testers attempt to exploit vulnerabilities to gain unauthorized access to systems and data. This can include password cracking, finding unpatched software flaws, and abusing misconfigurations.
- Analysis: The testers document all the vulnerabilities discovered and how they gained access. The vulnerabilities are categorized by severity.
- Reporting: The testers deliver a report of all findings, recommended solutions, and steps to improve security.
How often do I need Pen testing?
Most experts recommend performing penetration testing at least annually. More frequent testing every 6 or 3 months is ideal for organizations handling highly sensitive data. The frequency should also be determined by factors like:
- Infrastructure changes like new systems or cloud migrations
- Major application updates
- Increased cyber attack activity
- Regulatory compliance requirements
Annual testing of public facing systems and new applications before launch is a good starting point. Internal systems that store sensitive data should be tested more often.
Types of Pen testing
There are several types of penetration testing, categorized by the information provided to testers:
- Black box testing: Testers are provided no insider knowledge beyond the company name. They must thoroughly probe systems like real attackers.
- White box testing: Testers are given internal networks architecture, IP addresses, access credentials and more.
- Gray box testing: Testers have limited insider information combined with black box techniques.
Pen testing can also be categorized by target:
- Network pen testing: Attempting breaches on corporate networks and intranets.
- Web app pen testing: Finding flaws in websites and online applications.
- Mobile app pen testing: Testing mobile apps for vulnerabilities.
- Social engineering: Testing human elements like phishing susceptibility.
- Physical pen testing: Testing physical locations and devices.
How much do they cost?
The cost of pen testing services varies based on the size of the organization, scope of the tests and geography. Small businesses may pay anywhere from $1,500 to $10,000+ for an engagement. For large enterprises, costs can exceed $100,000 for comprehensive testing across multiple applications and locations.
Factors that influence pen testing pricing:
- Size of the IT infrastructure and assets: More assets means increased testing time.
- Type of testing: Black box testing takes more effort than white box.
- Skill level: Highly experienced pen testers charge more.
- Testing frequency: Frequent testing means companies can negotiate better rates.
- Industry: Heavily regulated industries like finance and healthcare pay more.
- Location: Pen testing for overseas assets costs more.
How to choose the top penetration testing company?
Here are some key considerations when selecting a penetration testing services provider:
Experience: The company should have seasoned professionals, not just basic automated scanners. Look for experience in your specific industry.
- Methodology: Ensure they take a structured, careful approach tailored to your environment vs generic tests.
- Reporting: Reports should provide technical details, proof-of-concepts, remediation advice and executive summaries.
- Reputation: Check reviews, brand reputation, thought leadership and recognitions. Companies with satisfied clients and industry awards are preferable.
- Credentials: Leading certifications like CEH, OSCP, GPEN, GWAPT demonstrate the technical expertise of the team.
- Communication: Choose testers who provide clear scoping, reporting and status updates instead of just results.
- Ethics: Work only with ethical, authorized pen testers, not freelancers hiring themselves out.
Top Penetration Testing Companies
Here are the top penetration testing companies to consider based on research and expert reviews:
Top Penetration Testing Companies – At a glance
| # | Company | Headquarters | Founded | Revenue | Employees | Services | Standout |
| 1 | Secureworks | Atlanta, GA | 1999 | $561 million (FY 2020) | Over 2200 | Application, network, cloud, red team testing | Part of Dell Technologies portfolio |
| 2 | Rapid7 | Boston, MA | 2000 | $326 million (FY 2020) | Over 1600 | App sec, dynamic pen testing, managed services | Nexpose, Metasploit, Insight platform |
| 3 | Invicti | Austin, TX | 2003 | $69 million (FY 2020) | 375 | SAST, DAST, IAST, SCA | Acunetix, Netsparker, web vulnerability scanner |
| 4 | Intruder | Melbourne, Australia | 2004 | $12.1 million (FY 2020) | 82 | Network, web, mobile app sec, red team | Specializes in finance industry |
| 5 | Cyberhunter | Dallas, TX | 2008 | $8.6 million (FY 2020) | 98 | Cloud, network, web app pen testing | State-level cyber ranges |
| 6 | Cobalt | San Francisco, CA | 2013 | $37.5 million (FY 2019) | 150 | Dynamic pen testing, phishing | Veteran-owned, used by Fortune 500s |
| 7 | ScienceSoft | McKinney, TX | 1989 | $50 million (FY 2020) | 1000 | Network, mobile, IoT testing | 1000+ security engineers |
| 8 | Raxis | Tampa, FL | 2002 | $42 million (FY 2020) | 400 | Web, network pen testing | Part of the KPGM portfolio |
| 9 | Redbot | Minneapolis, MN | 2015 | $15 million (FY 2020) | 82 | Web app sec, Kuberenetes pen testing | Specializes in tech sector |
| 10 | Acunetix | Malta | 2005 | $10 million (est) | 50 | SAST, DAST, vulnerability scanner | Used by NASA, Harvard, Adobe |
Best Penetration Testing Companies – Let’s dive deeper
1. Secureworks
Secureworks is a leading global cybersecurity company that protects organizations with offensive and defensive security solutions. They are part of the Dell Technologies portfolio.
- Founded: 1999
- Headquarters: Atlanta, GA
- Employees: Over 2200
- Revenue: $561 million (FY 2020)
- Services: Application, network, cloud, red team testing
- Clients: 20% of Fortune 100 companies
- Reviews: 4.2/5 on Gartner, 4.4/5 on Glassdoor
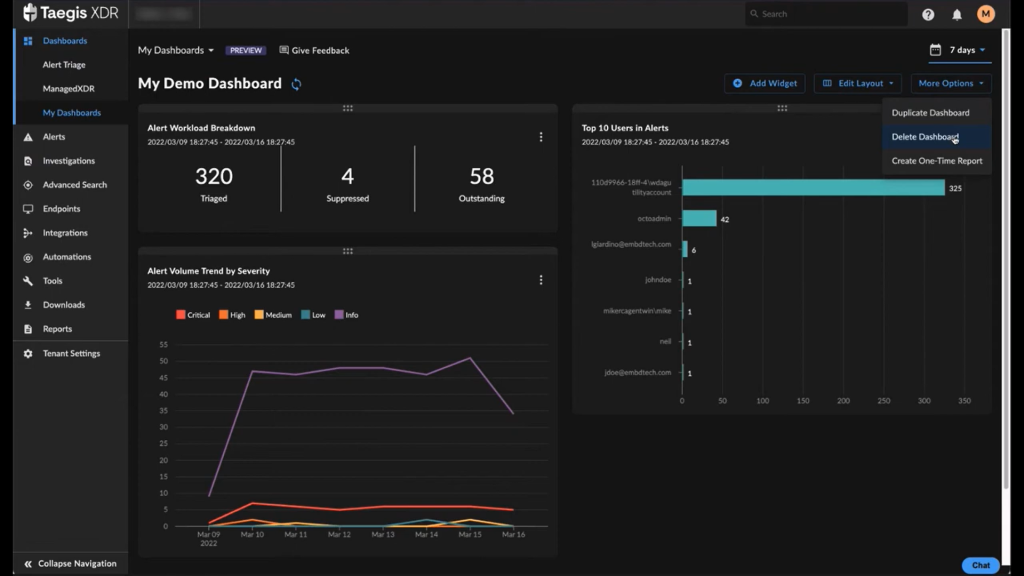
With over 20 years of experience, Secureworks is regarded as one of the top penetration testing companies globally. They have performed thousands of successful security tests across many industries like finance, healthcare, retail and technology. Secureworks takes an intelligence-driven approach to penetration testing. Their experts thoroughly study the client’s environment and threat landscape before beginning an attack simulation.
Secureworks has invested heavily in developing proprietary technologies to deliver more realistic and advanced adversarial testing. For example, their Hacker Ally platform can automate pen testing activities that are typically manual and time-intensive. Their red team exercises can effectively mimic the tactics and stealth of real-world attacks. Secureworks is known for providing very detailed reporting with clear remediation guidance. They also offer managed pen testing and other cybersecurity services. Their acquisition by Dell Technologies gives them access to superior resources and threat intelligence.
Key Features
- Proprietary Hacker Ally platform for automated pen testing
- Red team testing that emulates advanced persistent threats
- Focus on actionable reporting and CISO guidance
- Part of Dell Technologies gives access to superior capabilities
Why You Should Consider
With a large team of over 1000 security researchers and two decades of experience, Secureworks is an ideal choice for in-depth penetration testing of complex global infrastructures. Their services are on the higher end in terms of pricing, but provide great value for large enterprises.
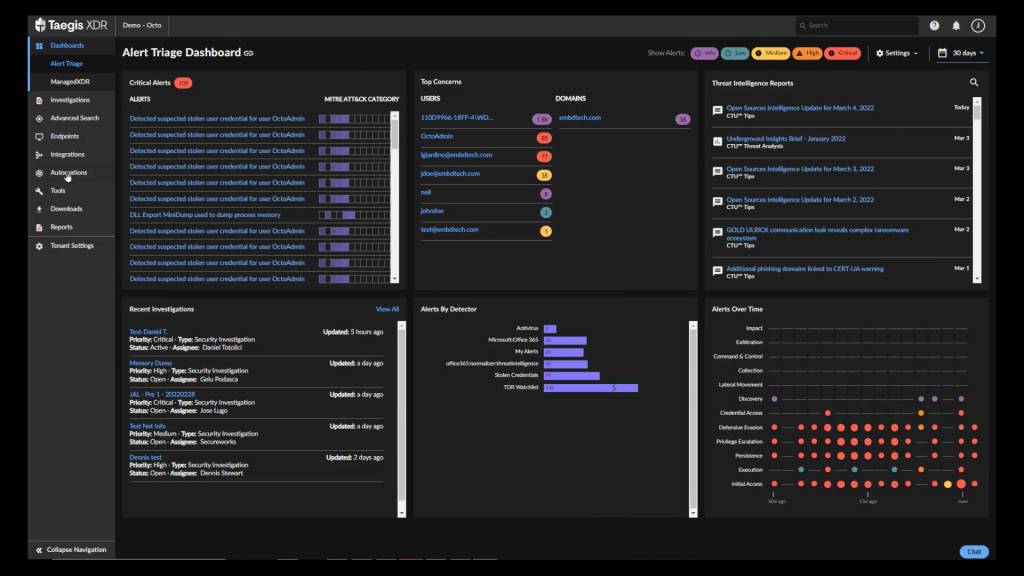
2. Rapid7
Rapid7 is a leading provider of cybersecurity and application security solutions. They are best known for their Nexpose vulnerability scanner and Metasploit penetration testing tool.
- Founded: 2000
- Headquarters: Boston, MA
- Employees: Over 1600
- Revenue: $326 million (FY 2020)
- Services: Application security, dynamic pen testing, managed services
- Clients: Fortune 100 companies, government agencies
- Reviews: 4.3/5 on Gartner, 3.6/5 on Glassdoor
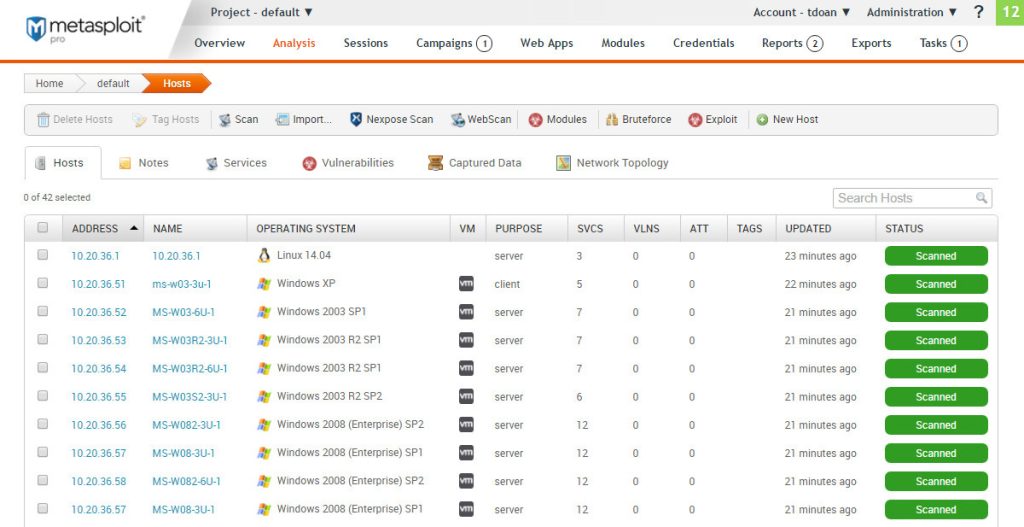
Rapid7 has established itself as a trusted cybersecurity partner for enterprises through its comprehensive suite of application security, incident detection and response solutions. The company is relied upon by Fortune 100 companies and government organizations around the world. Rapid7’s penetration testing services are highly regarded for their real-world attack simulation capabilities.
The company has strong roots in open source penetration testing tools like Metasploit. Their pen testing experts leverage this knowledge to find vulnerabilities and misconfigurations that automated scanners would miss. Rapid7 provides remediation guidance tailored to client environments and technology stacks. For dynamic and point-in-time testing, Rapid7 utilizes their Insight platform to identify vulnerabilities. Their managed pen testing offering provides continuous testing and risk monitoring.
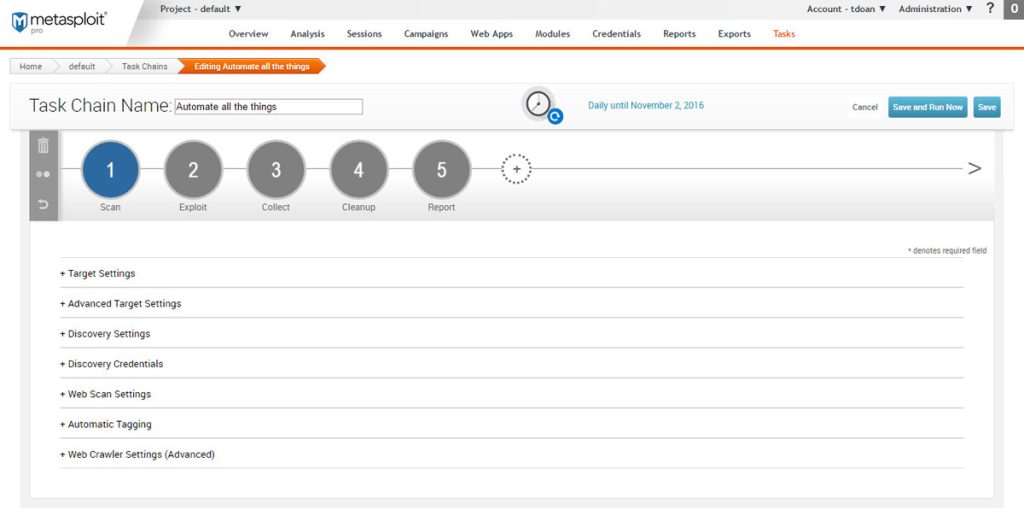
Key Features
- Real-world attack simulation based on expert knowledge
- Dynamic and continuous pen testing capabilities
- Detailed remediation guidance for discovered vulnerabilities
- Leverages Insight platform, Metasploit and Nexpose
Why You Should Consider
With experienced pen testers and proven dynamic testing capabilities, Rapid7 is a top choice for Fortune 500s and global organizations that need continuous assessment to manage risk.
3. Invicti
Invicti Security provides web vulnerability scanners and application security solutions. Their main products include Acunetix, Netsparker, and Acunetix SCADA.
- Founded: 2003
- Headquarters: Austin, TX
- Employees: 375
- Revenue: $69 million (FY 2020)
- Services: SAST, DAST, IAST, SCA
- Clients: NASA, Adobe, Harvard, Toyota, Stanford
- Reviews: 4.6/5 on Gartner, 4.2/5 on G2 Crowd
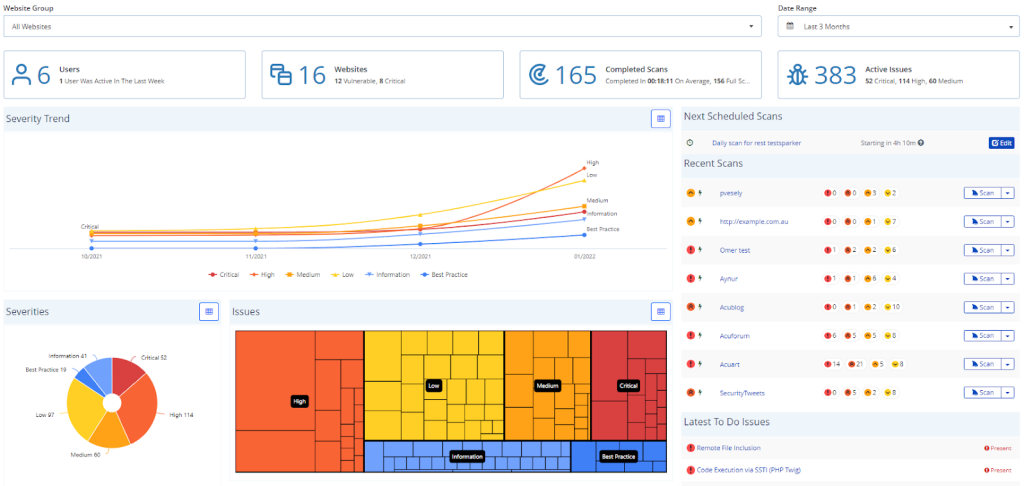
Invicti Security is dedicated to web and mobile application security. While they offer professional security testing services, Invicti’s main strength lies in their widely used vulnerability scanners. Their Acunetix scanner specializes in finding weaknesses in web applications using DAST techniques. Netsparker delivers static and interactive scanning capabilities for web and mobile apps.
Invicti’s team has years of experience performing web pen testing engagements across industries like finance, ecommerce, healthcare and education. Their testers are highly skilled at finding logic flaws, injection issues, misconfigurations and other OWASP top vulnerabilities. For large enterprises, Invicti provides dynamic pen testing, red team exercises and API security testing. Their detailed reports clearly explain how vulnerabilities can be exploited and fixed.
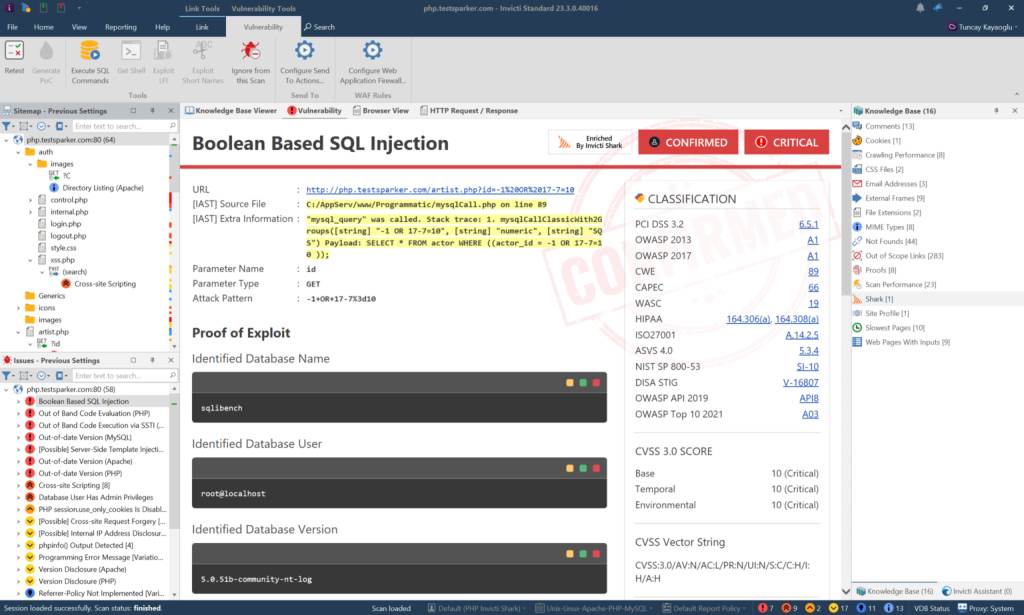
Key Features
- Acunetix and Netsparker vulnerability scanners
- Web and mobile application security expertise
- OWASP top 10 vulnerability detection
- API pen testing capabilities
Why You Should Consider
Invicti Security is a global leader in dynamic web application security testing. Their services paired with Acunetix and Netsparker provide complete application security capabilities.
4. Intruder
Intruder is an Australian cybersecurity company focused on penetration testing and vulnerability assessments. They mainly serve clients in the banking and financial services industry.
- Founded: 2004
- Headquarters: Melbourne, Australia
- Employees: 82
- Revenue: $12.1 million (FY 2020)
- Services: Network, web, mobile app sec, red team testing
- Clients: ANZ, Commonwealth Bank, Westpac, Vanguard
- Reviews: 5/5 on Google, 4.9/5 on Facebook
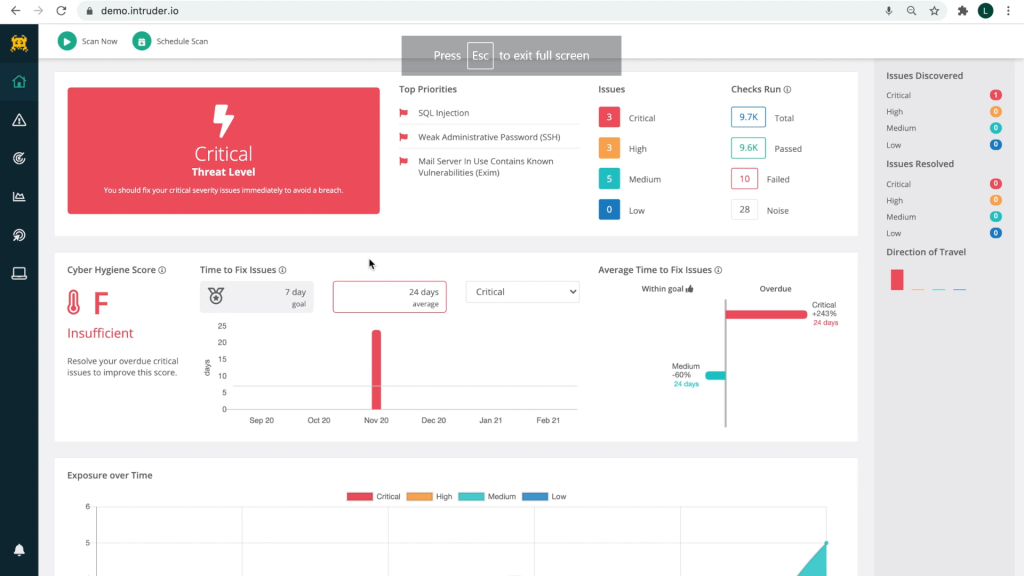
Intruder is a niche player that has deep expertise in penetration testing for the banking and finance sector. The company was founded by former government cybersecurity experts in Australia. Intruder’s pen testing capabilities cover networks, web applications, mobile apps and infrastructure. Their red team exercises emulate sophisticated real-world adversaries to test detection and response capabilities.
Given their specialization, Intruder’s consultants have an intimate understanding of financial application landscapes, compliance requirements, and data security needs. Their testing methodology is tailored to find flaws that pose the greatest risks to financial data. Intruder also offers cybersecurity training, risk advisory and managed security services built for the FSI. Their pentest reports provide evidence-based recommendations focused on risk reduction.
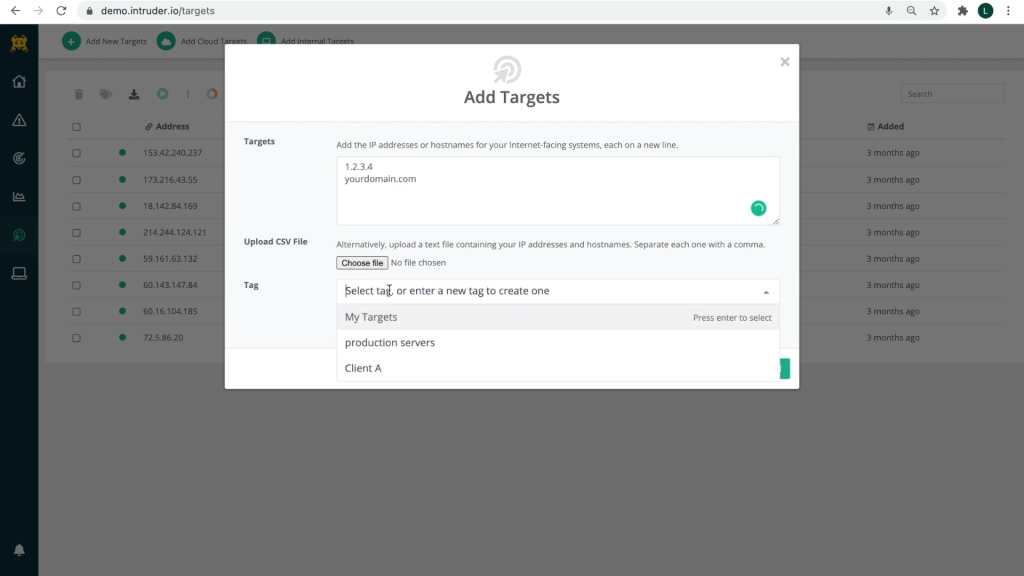
Key Features
- Specialized pen testing services for banking and FSI
- Red team testing with real-world attack simulation
- Built-in compliance with industry regulations
- Evidence-based reporting focused on risk mitigation
Why You Should Consider
Intruder is the top choice for banks, insurers and financial institutions that need specialized information security expertise.
5. Cyberhunter
Cyberhunter offers advanced cybersecurity services including penetration testing, vulnerability management and managed security. They focus on the banking, energy and telecom sectors.
- Founded: 2008
- Headquarters: Dallas, TX
- Employees: 98
- Revenue: $8.6 million (FY 2020)
- Services: Cloud, network, web app pen testing
- Clients: 250+ mid-sized organizations
- Reviews: 4.9/5 on Google, 4.8/5 on Facebook
Cyberhunter delivers comprehensive penetration testing services covering cloud infrastructure, networks, web applications, IoT devices and more. They are known for their private state-level cyber ranges that provide hyper-realistic testing environments. Cyberhunter’s cyber ranges allow complete attack simulations without impacting production systems.
The company focuses on continuous threat assessment and vulnerability management as opposed to one-off pentests. Their experts are skilled at finding weaknesses in custom web applications written in languages like .NET and Java. For cloud infrastructure, they test for misconfigurations on AWS, Azure and Google Cloud. Cyberhunter produces very detailed technical reports for both management and IT teams. They also provide virtual CISO services, security policy consulting and compliance audits.
Key Features
- Hyper-realistic cyber ranges for pen testing without production impact
- Continuous vulnerability assessments
- Specialized testing of cloud infrastructures
- Detailed technical and executive reporting
Why You Should Consider
Cyberhunter is an ideal choice for mid-sized companies that need comprehensive security testing paired with virtual CISO and compliance services.
6. Cobalt
Cobalt provides penetration testing and red team assessments. They focus exclusively on pen testing and have tested over 750 clients globally.
- Founded: 2013
- Headquarters: San Francisco, CA
- Employees: 150+
- Revenue: $37.5 million (FY 2019)
- Services: Dynamic pen testing, red team testing, phishing security
- Clients: Fortune 500s, tech unicorns, banks
- Reviews: 4.9/5 on Gartner, 4.6/5 on Crunchbase
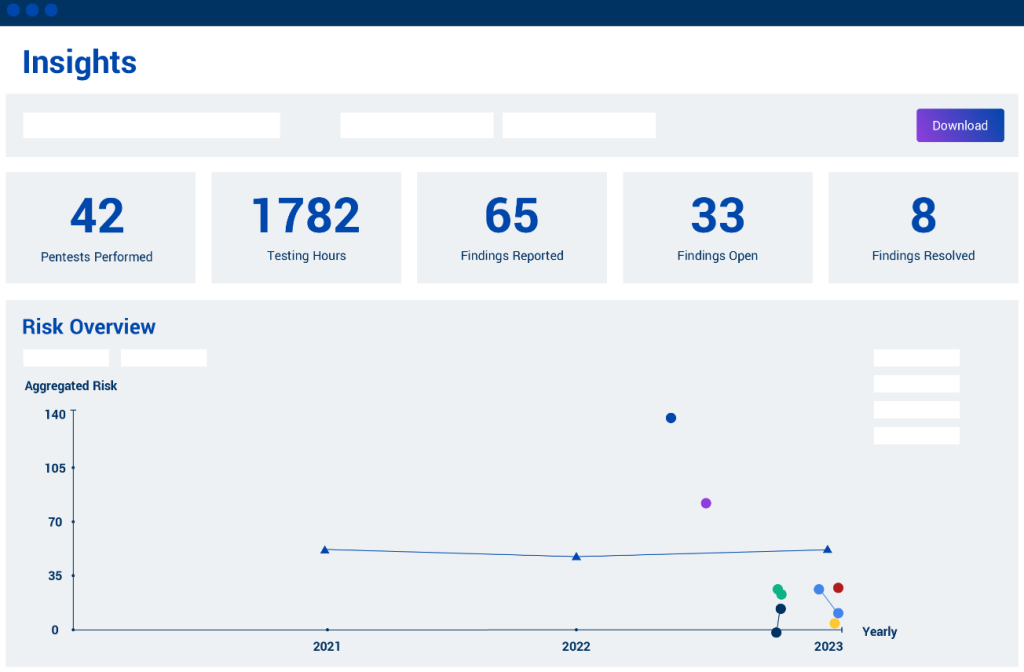
Cobalt takes an offensive approach to cybersecurity through real-world pen testing and targeted threat simulation. Instead of compliance checklists, Cobalt’s experts focus on practical attack scenarios tailored to the client’s industry and risk profile. Their red team exercises mimic motivated adversaries over a long period to assess detection capabilities.
Cobalt’s pen testers are highly skilled at compromising traditional and modern environments including cloud, containers, APIs and web apps. Their testing spans networks, hosts, credentials, usernames, external assets and anything exposed. Post-engagement, Cobalt delivers simple executive reports as well as detailed technical breakdowns of all discoveries. Being a veteran-owned business, Cobalt offers its services at below-market rates for government agencies.
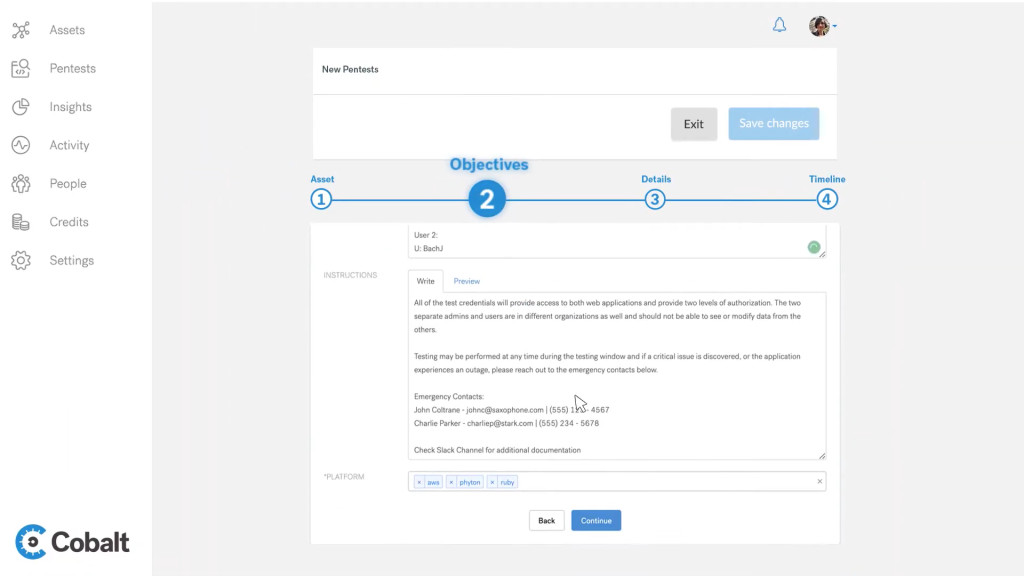
Key Features
- Real-world attack simulation based on industry threat profiles
- Red team testing over an extended period
- Expertise in cloud, API and microservices testing
- Detailed technical reporting on vulnerabilities
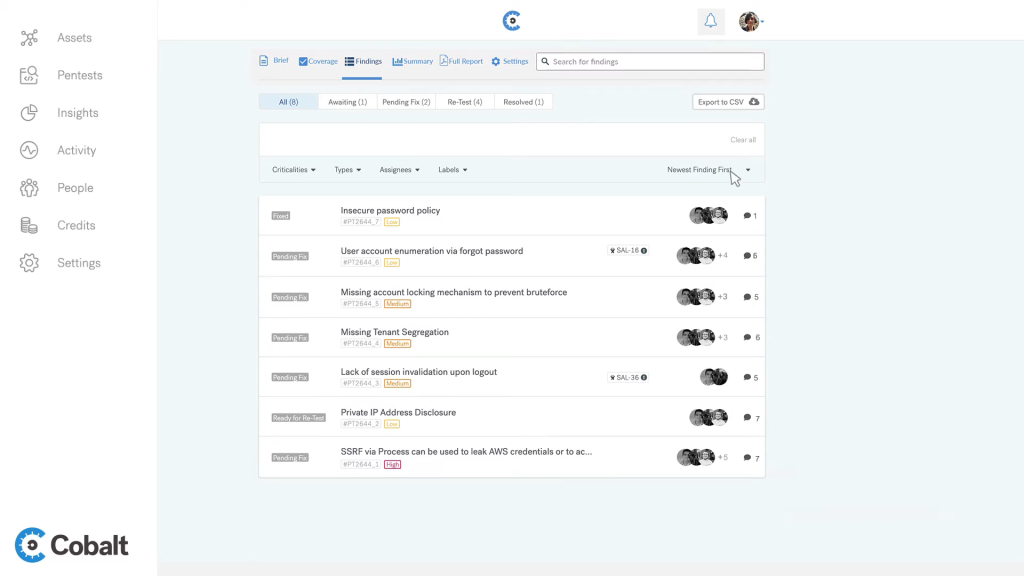
Why You Should Consider
Cobalt is the top choice for Fortune 500s and unicorns that need dynamic pen testing tailored to their specific risk environment. Their veteran-owned business background also makes them a good fit for government and military testing projects.
7. ScienceSoft
ScienceSoft is an IT consulting and services company with over 1000 engineers. They offer security testing and consulting services for enterprises.
- Founded: 1989
- Headquarters: McKinney, TX
- Employees: 1000
- Revenue: $50 million (FY 2020)
- Services: Network, mobile, IoT testing
- Clients: Nestle, NASA, Boeing, IBM
- Reviews: 4.6/5 on Clutch, 5/5 on GoodFirms
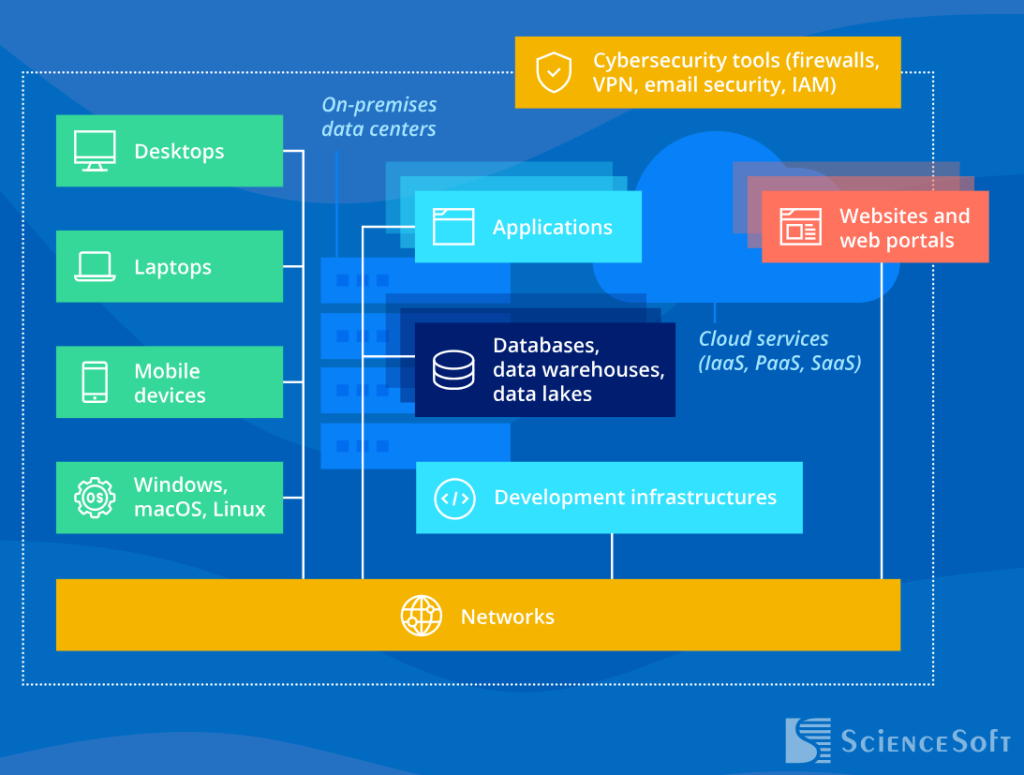
ScienceSoft has been providing software development and testing services for over 30 years across industries like telecom, manufacturing, finance and healthcare. Their security testing services are focused on networks, mobile, IoT and embedded systems.
ScienceSoft’s network penetration testing covers external, internal, wireless and VoIP networks. Their experts are skilled at pivoting across network segments and escalating privileges. For mobile apps, ScienceSoft evaluates authentication, encryption and platform interaction flaws. Their IoT testing is geared towards smart devices and industrial systems. Compliance audits for HIPAA, PCI DSS and other standards can be added on. Being a large software engineering firm, ScienceSoft can seamlessly transition from pen testing to remediation and development.
Key Features
- Network penetration testing and pivoting
- Testing of mobile apps, IoT and embedded devices
- Source code audits for insecure coding risks
- End-to-end services including remediation and software dev
Why You Should Consider
ScienceSoft provides integrated security assessment and software engineering services under one roof, making them ideal for product companies. Their testing expertise spans modern environments including cloud, containers, IoT, mobile and web apps.
8. Raxis
Raxis provides application security, penetration testing and identity management services. They are part of the Kyndryl partner network.
- Founded: 2002
- Headquarters: Tampa, FL
- Employees: 400
- Revenue: $42 million (FY 2020)
- Services: Web, network pen testing
- Clients: Auto, banking, healthcare, retail
- Reviews: 5/5 on Clutch, 4.9/5 on Facebook
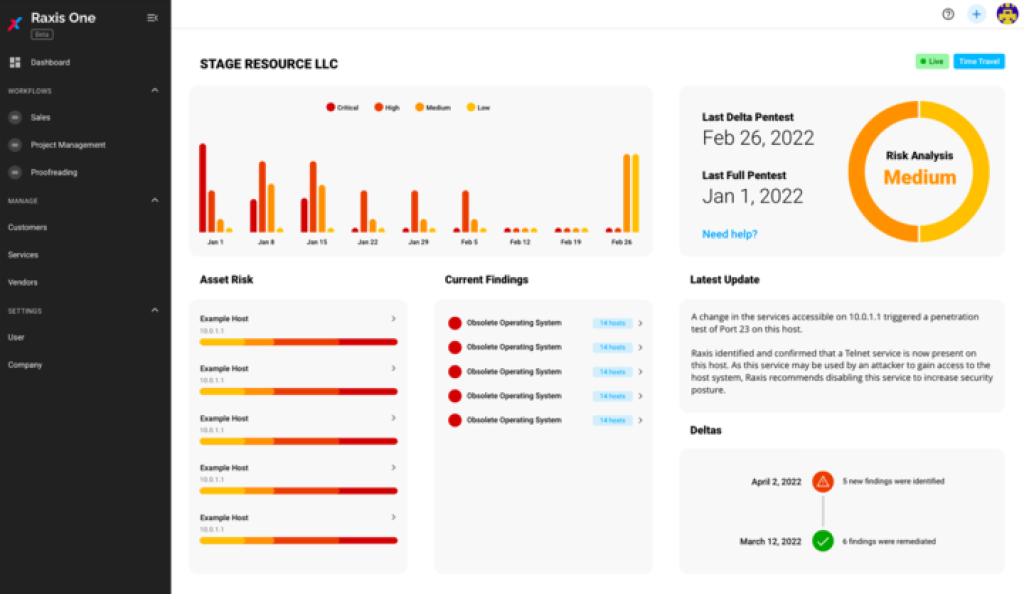
Raxis approaches pen testing from the perspective of professional hackers. Their experts think creatively to identify unknown vulnerabilities and exposure points that put client data and infrastructure at risk. Raxis provides web and network penetration testing for companies across industries like finance, retail, higher education and healthcare.
For web application testing, Raxis covers OAuth, logic flaws, injections, encryption and access control issues. Network pen testing spans external, internal and cloud networks to find misconfigurations and weaknesses. Their experts are highly skilled with tools like Metasploit, Burp Suite and Kali Linux. Raxis also offers security training and advisory services focused on risk reduction. Being part of Kyndryl gives them access to advanced testing labs and platforms.

Key Features
- Creative black box testing methodology
- Web and network pen testing capabilities
- Hands-on security training for developers
- Part of the Kyndryl partner ecosystem
Why You Should Consider
Raxis brings experienced pen testing consultants and an out-of-the-box approach to uncovering hard-to-find vulnerabilities, making them a great choice for companies looking to strengthen security posture.
9. Redbot Security
Redbot Security provides application and infrastructure penetration testing for tech companies and startups.
- Founded: 2015
- Headquarters: Minneapolis, MN
- Employees: 82
- Revenue: $15 million (FY 2020)
- Services: Web app sec, Kubernetes pen testing
- Clients: Tech unicorns and startups
- Reviews: 5/5 on Clutch, 4.8/5 on Crunchbase
Redbot delivers extensive penetration testing tailored for tech companies building software products and SaaS platforms. Their services are designed for modern tech stacks including cloud, containers, APIs and web apps. Redbot focuses on simulating highly motivated attackers attempting to breach and pivot across cloud assets.
For web and mobile apps, Redbot evaluates authentication, data handling, encryption and access control vulnerabilities. Their experts are highly skilled at breaching and escalating privileges in cloud infrastructure on AWS, Azure and Google Cloud. Redbot also provides Kubernetes pen testing to find risks in container environments. Their reports are geared towards remediation with action items mapped to owners. Being a tech company themselves, Redbot understands the developer mindset and provides guidance accordingly.
Key Features
- Specialized pen testing for SaaS and cloud-native companies
- Real-world attack simulation across cloud environments
- Kubernetes and container security evaluations
- Detailed reports tailored for developer remediation
Why You Should Consider
Redbot brings deep expertise in testing modern tech stacks and cloud environments, making them the top choice for software companies and tech startups.
10. Acunetix
Acunetix provides web vulnerability scanning and network security testing solutions used by Fortune 500 companies.
- Founded: 2005
- Headquarters: Sliema, Malta
- Employees: 50+
- Revenue: $10 million (estimated)
- Services: SAST, DAST, vulnerability scanner
- Clients: NASA, Harvard, Adobe, Dropbox
- Reviews: 4.6/5 on Capterra, 4.4/5 on G2 Crowd
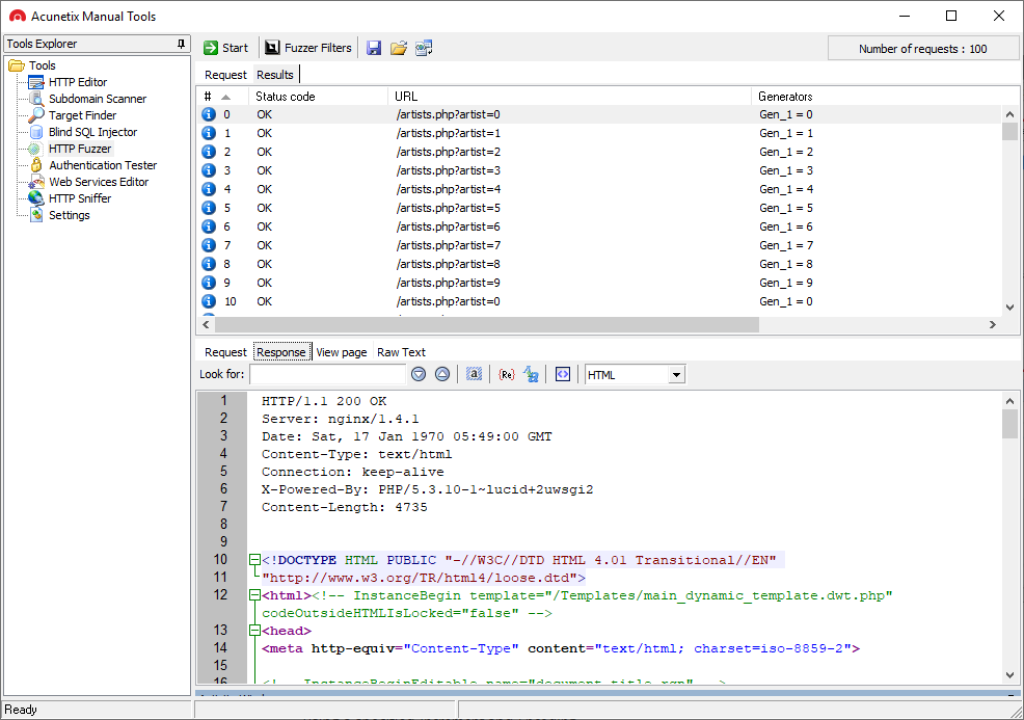
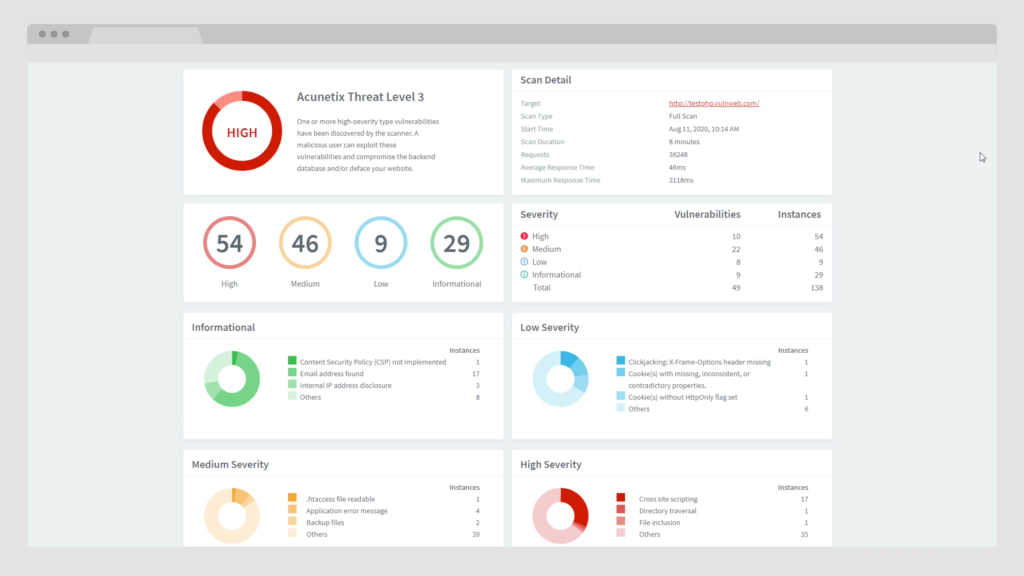
Acunetix offers advanced web vulnerability scanning capabilities used by some of the world’s leading companies. Their Acunetix scanner dynamically detects over 4000 web vulnerabilities covering OWASP top 10 risks, code injections, XSS flaws and more.
For manual testing, Acunetix provides network security scanning and PCI compliance assessment. Their network scanner covers denial of service, device detection, open ports and services. Acunetix consultants also perform manual web and network penetration testing leveraging the advanced scanning capabilities. Extras like malware monitoring, site crawler and productivity tools add value.
Being developer-friendly, Acunetix offers integration support for IDEs, CI/CD pipelines, WAFs and GRC platforms. Their detailed scan reports include proof of concepts and remediation guidance. Acunetix caters to large enterprises that need scalable and automated scanning across global web environments.
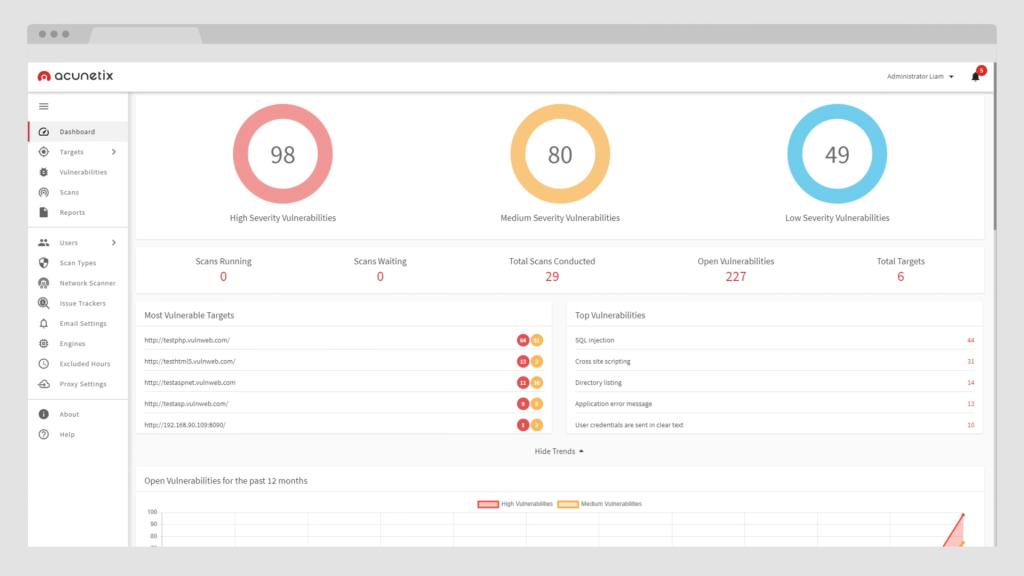
Key Features
- Acunetix web vulnerability scanner
- Network security scanning
- Highly accurate vulnerability detection
- Integrations with developer tools
- Scalable scanning for large environments
Why You Should Consider
With advanced automated scanners and developer-focused features, Acunetix is ideal for large companies looking for scalable, accurate and continuous vulnerability scanning.
FAQs
What’s the difference between a penetration test and a vulnerability scan?
A vulnerability scan only looks for known weaknesses and misconfigurations based on an automated database of flaws. A penetration test goes beyond scanning to actively exploit systems and applications in an attempt to gain access and evaluate real-world exposure. Pen testing provides a more comprehensive assessment mimicking real hackers.
Are penetration tests disruptive to regular operations?
Reputable penetration testers follow strict rules of engagement and target clones of production systems when feasible to avoid downtime risks. Some highly advanced red team tests can briefly impact operations, but testers will coordinate closely with IT teams to minimize disruption. The benefits of finding major flaws before hackers do far outweighs temporary issues.
Can a penetration test guarantee the security of my systems?
Penetration tests assess the security posture at one point in time and find many vulnerabilities, but cannot guarantee protection. Security requires ongoing vulnerability management, patching, training and testing. Penetration testing combined with multifactor defenses provides the best security.
What is included in a penetration testing report?
Quality pen test reports include a executive summary, detailed findings, proof-of-concept attacks, severity grades for flaws, recommendations for fixing vulnerabilities, and technical details for IT teams. The reports allow both leadership and technical teams to understand and improve security protections.
Conclusion
Regular penetration testing by skilled professionals is one of the best investments organizations can make to improve security. Testing proactively identifies vulnerabilities and weaknesses before malicious hackers can find and exploit them. With constant threats and evolving attack techniques emerging daily, comprehensive security assessments have become absolutely essential.
This guide provided an overview of the top penetration testing companies that organizations can partner with to strengthen their security posture. Leading pen testing providers like Secureworks, Rapid7, Invicti and others differentiate themselves through experienced consultants, methodical processes, detailed reporting and insights tailored to enhance security based on industry best practices. With regular pen testing combined with robust cybersecurity policies and controls, companies can manage risks effectively.